What is an Internal Network Penetration Test?
Internal network penetration testing evaluates the security of an organization's internal network by simulating an insider threat or an attacker who has already breached the external defenses and gained access to the internal network. This type of testing focuses on identifying vulnerabilities that could be exploited to escalate privileges, access sensitive data, or disrupt operations within the internal network. The goal is to assess the organization's internal security posture and to identify weaknesses that could be leveraged by malicious insiders or attackers with initial access.
Penetration testers performing internal network testing typically start by mapping the internal network, identifying key systems, and discovering potential attack vectors. They may use techniques such as network sniffing, credential harvesting, and privilege escalation to achieve their objectives. Common vulnerabilities that may be identified include weak internal authentication mechanisms, insufficient network segmentation, outdated software, and misconfigured security controls. The results of the testing are compiled into a comprehensive report, which includes detailed findings and recommendations for improving internal security measures. The ultimate objective is to enhance the organization's resilience against internal threats and to protect critical assets and data.
Frameworks and Standards
NIST SP 800-115: A technical guide to information security testing and assessment.
PTES: Provides a lifecycle for penetration testing engagements.
Common Tools we utilize to assess your Internal Network:
Nmap: Used for network discovery and enumeration.
Metasploit Framework: An exploitation framework used to test vulnerabilities.
Nessus: A vulnerability scanner to identify known security issues.
Responder: A tool for LLMNR, NBT-NS, and MDNS poisoning.
Wireshark: A network protocol analyzer for network traffic analysis.
Let Rarefied help assess your internal network today!
How a Security Test is Performed
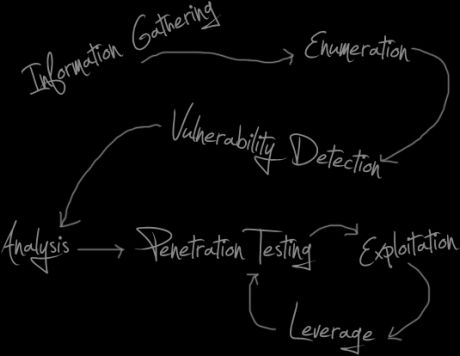
Our penetration testing methodology is based on a variety of security standards including, but not limited to, NIST, OWASP, and industry best practices. We put each target through this process to ensure a quality test every time and to meet our service commitments. Our test results can be used to support compliance standards (PCI, HIPAA, etc.) or best practices.
01
Information Gathering & Enumeration
This is the most crucial stage of the assessment. In this phase, we learn everything we can about your environment by assessing technologies used, possible attack points, open ports, and anything else publicly discoverable. What we find here serves as the baseline for all future tests.
02
Vulnerability Detection
We use a hybrid approach of manual testing techniques and automated scanning tools to look for possible vulnerabilities in your environment.
03
Analysis
Now it's time to develop a plan. Based on what we have learned up to this point, we decide which attack vectors to further pursue, and start testing.
04
Vulnerability Exploitation & Leverage
This is where the real fun begins. A successful attack is almost always the result of chaining vulnerabilities together until the target is fully compromised. This is typically a circular process, in which vulnerabilities are tested for, exploited, and then leveraged to test for more issues. The process repeats itself until the goal is achieved.
We deliver a formal report detailing our findings
We'll test your web applications, network hosts, APIs, and mobile applications for security issues. We'll then discuss the issues with your team and provide a report detailing our findings. This report can be used in support of compliance (PCI, HIPAA, etc.) or best practices.
What comes next?
Once we have completed our testing, we'll work closely with your team to make sure they understand the issues we have uncovered. Our goal is to ensure that our rigorous security testing provides you and your team with peace of mind that you are implementing secure coding techniques correctly and following security best practices effectively.
Ready to get started?
We look forward to discussing your security testing needs.